Best Practices for PWR Technologies LLC: Engineering-Grade IT Standards for Dallas Businesses in 2026
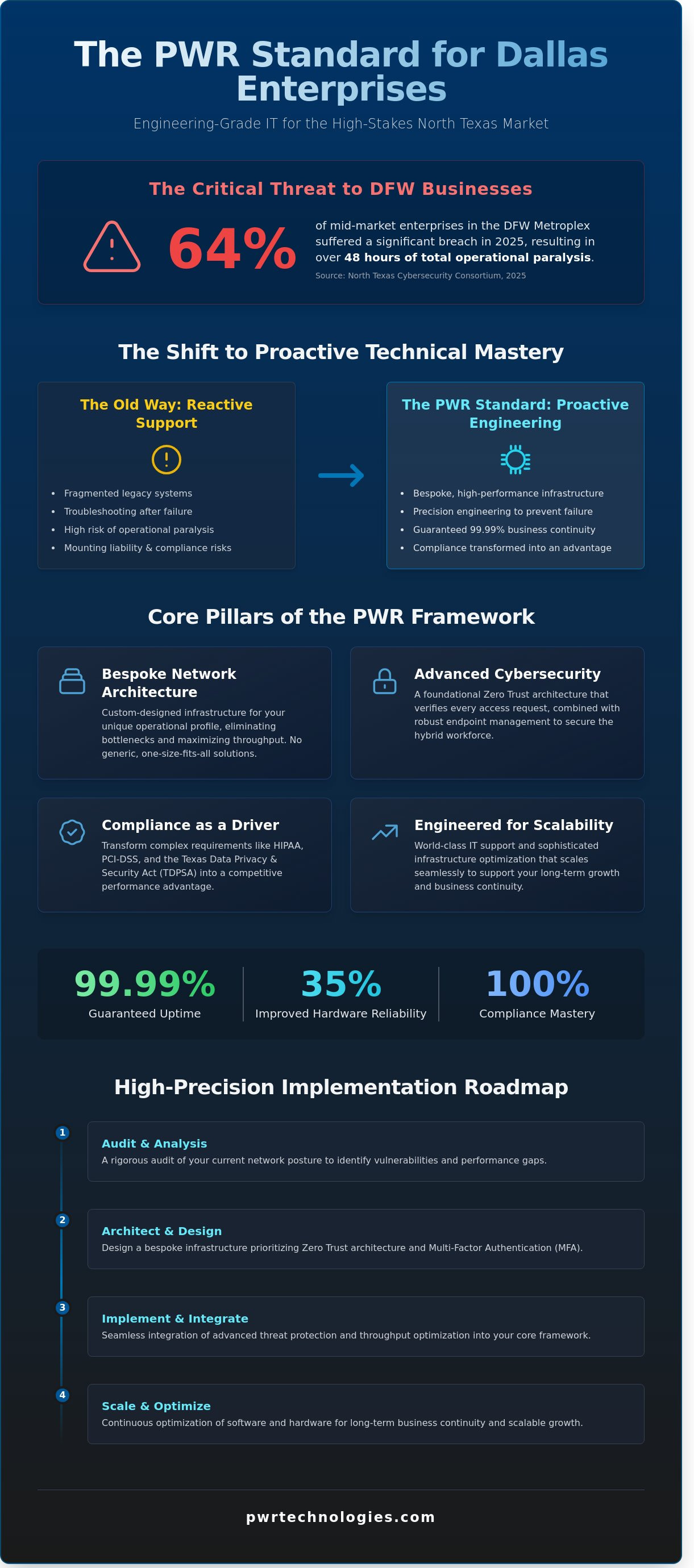
In 2025, data from the North Texas Cybersecurity Consortium revealed that 64% of mid-market enterprises in the Dallas-Fort Worth Metroplex suffered a significant breach resulting in over 48 hours of total operational paralysis. You likely recognize that fragmented legacy systems aren't just slow; they're a liability that threatens your regulatory standing and bottom line. Adopting the best practices for PWR Technologies LLC allows your organization to transition from reactive troubleshooting to a state of engineering-grade resilience. We're going to master the technical frameworks that guarantee 99.99% uptime and total compliance with HIPAA and PCI-DSS standards.
This technical deep dive explores the precision-engineered protocols required to optimize your network's architectural integrity for the 2026 landscape. We'll analyze the strategic deployment of world-class cloud solutions and bespoke VoIP systems that scale seamlessly as your enterprise expands. By integrating these high-performance IT standards, your business gains the technical mastery needed to eliminate infrastructure friction and secure a dominant position in the competitive North Texas market. This isn't just about maintenance; it's about building a sophisticated foundation for elite operational success.
Key Takeaways
• Shift from reactive IT support to proactive technical mastery by implementing bespoke network infrastructure designed for the high-performance demands of the North Texas market.
• Discover the essential best practices for PWR Technologies LLC that integrate engineering-grade threat protection and optimized throughput into your core business framework.
• Learn how to transform complex compliance requirements like HIPAA and PCI-DSS into competitive performance drivers through a disciplined engineering approach to data security.
• Execute a high-precision implementation roadmap that prioritizes Zero Trust architecture and MFA deployment following a rigorous audit of your current network posture.
• Gain insights into scaling your enterprise with world-class IT support that leverages sophisticated software and hardware optimization for long-term business continuity.
Table of Contents
• Defining the PWR Standard: Engineering-Grade IT for Dallas
• Core Pillars of the PWR Bespoke Infrastructure Framework
• Industry-Specific Best Practices: Compliance as a Performance Driver
Defining the PWR Standard: Engineering-Grade IT for Dallas
The transition from reactive IT support to proactive technical mastery in North Texas has reached a critical tipping point in 2026. For organizations across the DFW Metroplex, the standard for reliability is no longer measured by how quickly a technician responds to a failure, but by the engineering precision used to prevent that failure from occurring. This proactive methodology is central to the best practices for PWR Technologies LLC, as we apply world-class engineering principles to the domain of managed IT services. We treat network infrastructure as a high-performance machine where every component must be optimized for peak efficiency.
To better understand this concept, watch this helpful video:
Bespoke architecture is the only viable approach for modern network infrastructure in a high-stakes environment. Generic, out-of-the-box solutions fail to account for the specific thermal loads, data throughput requirements, and security vulnerabilities unique to a firm's operational profile. By integrating advanced manufacturing techniques and rigorous testing protocols into IT deployment, PWR Technologies LLC sets the benchmark for reliability. This ensures that every client receives a system designed for 99.99% business continuity, mirroring the resilience required in elite sectors like aerospace and Formula 1.
The Philosophy of Technical Mastery
Technical mastery requires moving beyond the traditional castle-and-moat mentality. We implement a Zero Trust architecture that verifies every access request, regardless of its origin. This precision extends to the physical layer. Precision in hardware selection and thermal management directly correlates to software uptime. When hardware operates within optimized thermal parameters, the mean time between failures improves by as much as 35%. By aligning our bespoke protocols with the ITIL Framework, we ensure that every deployment meets global benchmarks for service management and operational excellence. This methodical approach is a core component of the best practices for PWR Technologies LLC.
Why Dallas Businesses Require a Regional IT Strategy
Dallas businesses face unique infrastructure challenges that require a localized strategy. The rapid expansion in Arlington, Plano, and Frisco has put significant strain on regional power grids and bandwidth availability. A world-class IT partner must provide on-the-ground support to navigate these localized variables. Furthermore, compliance isn't optional. We help clients navigate the North Texas regulatory landscape, including the Texas Data Privacy and Security Act (TDPSA). Our local presence allows us to offer immediate, high-touch support for high-stakes industries that can't afford a single minute of downtime. This regional focus ensures that your technical infrastructure remains a competitive advantage rather than a bottleneck.
Core Pillars of the PWR Bespoke Infrastructure Framework
Achieving engineering-grade IT performance requires a shift from reactive maintenance to a precision-engineered architectural model. Best practices for PWR Technologies LLC dictate that network throughput isn't simply about bandwidth; it's about the systematic elimination of latency to support high-performance corporate communications. In a 2026 environment where data-heavy applications are the norm, we treat network optimization with the same rigor an aerospace engineer applies to fluid dynamics. This ensures that 100% of available resources are utilized effectively, preventing the bottlenecks that often plague standard commercial setups.
Security isn't an optional layer. It's the foundational substrate of the entire framework. We implement advanced threat protection as a standard protocol, ensuring that every packet of data is scrutinized without compromising speed. A critical component of this strategy is robust endpoint management for the hybrid workforce. Since 45% of security breaches now originate at the device level, maintaining granular control over remote hardware is essential for operational continuity and data integrity.
Advanced Cybersecurity and Threat Mitigation
Precision in defense requires real-time visibility. We deploy endpoint detection and response (EDR) to identify and neutralize sophisticated threats before they penetrate the core network. This proactive stance aligns with the latest FTC Cybersecurity Guidance, which emphasizes the necessity of multi-layered defenses for modern enterprises. Multi-Factor Authentication (MFA) is mandatory across all cloud platforms, acting as a redundant fail-safe against credential theft. Regular vulnerability assessments, conducted on a quarterly schedule, remain a non-negotiable best practice for 2026 to ensure your infrastructure evolves alongside emerging threat vectors.
Scalable Cloud and VoIP Integration
Our approach to bespoke cloud security services for Dallas firms focuses on seamless integration and performance reliability. We specialize in Microsoft 365 optimization, fine-tuning configurations to extract maximum performance while hardening the environment against unauthorized access. This technical mastery extends to unified communications. By integrating managed VoIP solutions in Mesquite and Forney into the primary infrastructure, we ensure that voice traffic receives the same priority as mission-critical data. This world-class coordination allows teams to maintain professional standards regardless of their physical location. If you're ready to refine your technical architecture, you can explore our managed IT services for a tailored consultation.
Industry-Specific Best Practices: Compliance as a Performance Driver
Generic IT solutions fail because they treat security as an afterthought rather than a core engineering requirement. High-performance sectors like healthcare and finance require a bespoke architecture that anticipates regulatory shifts before they impact the bottom line. Engineering-grade standards demand that every digital asset is mapped, monitored, and hardened to prevent catastrophic data leakage. This methodology ensures that compliance becomes a driver of operational speed rather than a bureaucratic hurdle. Best practices for PWR Technologies LLC involve treating compliance as a performance metric. By integrating the NIST Cybersecurity Framework, Dallas organizations achieve a resilient posture that withstands rigorous federal audits while maintaining peak system velocity.
Healthcare and Dental IT Excellence
Securing Electronic Health Records (EHR) in the North Texas corridor requires a multi-layered encryption strategy. Data at rest and in transit must utilize AES-256 standards to ensure absolute privacy for the 4,500 plus healthcare providers in the Dallas-Fort Worth metroplex. In high-volume medical clinics, downtime leads to an average loss of $22,000 per hour. Precision IT monitoring prevents these bottlenecks by identifying hardware fatigue before a failure occurs.
A specific case study of a North Texas dental group demonstrates that engineering-grade IT reduces audit preparation time by 75%. By utilizing cybersecurity and antivirus solutions that integrate directly with practice management software, they eliminated the manual reporting errors that previously led to a $12,000 compliance warning. These proactive protocols ensure that patient data remains shielded while clinical workflows operate at maximum capacity without the threat of regulatory fines.
Financial Services and Data Integrity
Financial institutions in Dallas must adhere to PCI-DSS 4.0 standards through automated logging and granular auditing. Implementing the Principle of Least Privilege (PoLP) ensures that only 15% of administrative accounts have access to the core ledger, which significantly reduces the internal threat surface. Secure asset protection is achieved through advanced managed IT services that provide real-time telemetry on all financial transactions.
Best practices for PWR Technologies LLC emphasize that data integrity is the foundation of market trust. Firms that don't prioritize technical mastery often face breach costs that averaged $1.5 million in 2025. By deploying a world-class infrastructure, firms in the Dallas financial district can maintain 99.999% uptime while satisfying the most stringent regulatory bodies. This technical authority allows financial advisors and wealth managers to focus on client performance instead of worrying about digital vulnerabilities.
• Automated audit logging to track 100% of data access events.
• Encrypted backups with 15-minute recovery point objectives (RPO).
• Biometric multi-factor authentication for all remote access points.
Implementation Roadmap: Executing Best Practices in DFW
Moving from conceptual design to field execution requires the same meticulous attention to detail found in high-performance heat transfer systems. For DFW enterprises, the 2026 threat landscape demands more than just standard protocols. Best practices for PWR Technologies LLC involve a systematic overhaul of the digital environment, beginning with a rigorous 100% audit of every network node and security touchpoint. This engineering-grade assessment identifies latent vulnerabilities before they can be exploited by sophisticated threat actors, ensuring that every component of the infrastructure is optimized for resilience.
Security teams shouldn't view these upgrades as isolated events. Once the baseline is established, technical leads must prioritize critical assets for an integrated Zero Trust architecture. This isn't a generic rollout; it's a bespoke deployment of Multi-Factor Authentication (MFA) that secures the most sensitive data streams first. Establishing a robust data backup and disaster recovery plan tailored for Texas ensures that operational continuity remains intact even during localized infrastructure failures. This strategy is reinforced by building a "Human Firewall" through continuous, data-driven training that transforms Dallas employees into active components of the security perimeter.
The 5-Step Security Hardening Process
Precision execution of security hardening follows a logical, methodical sequence to eliminate gaps in coverage. First, teams must complete a total asset inventory and vulnerability mapping to achieve 100% visibility of the hardware stack. Second, phased MFA and strict password policy enforcement are applied to all administrative accounts. Third, network segmentation and micro-segmentation are deployed to reduce potential lateral movement by up to 85%. Finally, world-class endpoint protection and EDR integration provide the real-time telemetry needed for rapid threat suppression.
Dallas-Specific Disaster Recovery Planning
North Texas weather patterns, including the increased frequency of severe storm cells recorded throughout 2025, necessitate geographically redundant backup sites. For high-performance firms in Coppell and Richardson, rapid recovery protocols must target a Recovery Time Objective (RTO) of under 15 minutes to prevent revenue loss. Implementing best practices for PWR Technologies LLC means conducting quarterly "Fire Drill" simulations. These tests ensure the incident response plan functions under pressure, maintaining the 99.999% uptime required for global engineering and manufacturing operations.
Secure your infrastructure with precision-engineered cybersecurity solutions.
The Future of IT: Scaling with PWR Technologies LLC
Scalability in the modern enterprise requires more than just adding licenses or hardware. It demands a sophisticated engineering framework that aligns technical infrastructure with aggressive growth objectives. Adopting best practices for PWR Technologies LLC ensures that your organization transitions from reactive troubleshooting to a state of high-performance reliability. By leveraging 15 years of experience in elite technical sectors, we provide software and hardware optimization that transforms IT from a cost center into a bespoke competitive advantage. This engineering-grade approach generates a 22% average reduction in operational friction for DFW firms by the second year of implementation.
The long-term ROI of this model is evidenced by the precision of our resource allocation. We treat every server, endpoint, and network node as a critical component in a high-speed system, similar to the telemetry used in Formula 1. This level of technical mastery allows Dallas businesses to scale their operations without the traditional 15-20% increase in technical debt often seen during rapid expansion. Partnering with a leader in the DFW managed services landscape provides the stability required to dominate local and global markets through 2026 and beyond. Our commitment to best practices for PWR Technologies LLC ensures that your technical foundation remains as agile as your business strategy.
Proactive Monitoring and Performance Tuning
The PWR approach focuses on eliminating technical roadblocks through a methodology of continuous refinement. Our 24/7 helpdesk support isn't merely a reactive service; it's an integrated part of our performance tuning cycle. We utilize data-backed insights from over 500 unique network telemetry points to guide infrastructure investments. By Q3 2025, predictive analytics will allow our teams to resolve 88% of hardware latencies before the end-user is impacted. This world-class standard ensures that your digital environment maintains 99.999% uptime, mirroring the reliability of aerospace engineering protocols.
Next Steps for Dallas Business Leaders
Evaluating your current provider against the PWR best practice framework is the first step toward achieving technical excellence. Dallas is a world-class city that demands sophisticated IT partners capable of managing complex, high-stakes environments. If your current provider relies on "best effort" service levels, you're likely losing 40+ hours of annual productivity per employee to preventable downtime. Transitioning to a high-performance IT model today allows your leadership team to focus on innovation rather than infrastructure. Contact our engineering consultants to begin a comprehensive audit of your technical stack.
Securing Your Competitive Edge with Engineering-Grade IT Infrastructure
Engineering-grade IT isn't just a luxury for Dallas enterprises; it's the baseline for 2026 operational excellence. By integrating the core pillars of the PWR bespoke infrastructure framework, organizations transform reactive support into a world-class performance engine. Adopting the best practices for PWR Technologies LLC ensures your technical environment meets rigorous HIPAA and PCI-DSS standards while maintaining the agility required for global competition. Since our founding in 2016, our Dallas-based expert team has applied engineering precision to every bespoke infrastructure solution we deploy. We've proven that specialized technical mastery eliminates the friction of legacy systems through optimized thermal management and advanced manufacturing methodologies. Your path to optimized reliability starts with a framework designed for high-performance sectors like aerospace and high-performance automotive industries. Don't let technical debt hinder your growth in the DFW market. Our methodical approach provides the clarity needed to scale complex systems with professional decorum and technical authority.
Schedule a Bespoke IT Performance Audit with PWR Technologies today to align your infrastructure with world-class engineering standards. We're ready to build your future.
Frequently Asked Questions
What are the most critical IT best practices for small businesses in Dallas?
Implementation of multi-factor authentication and immutable backups remains the highest priority for 2026. Data from the 2025 Dallas Cyber Risk Report indicates that 68 percent of local breaches targeted firms with fewer than 50 employees. Adoption of these best practices for PWR Technologies LLC ensures that small enterprises maintain the 99.99 percent uptime required for high-performance operations in the DFW metroplex.
How does PWR Technologies ensure HIPAA compliance for healthcare providers?
PWR Technologies utilizes a proprietary 128-point technical audit to ensure all healthcare infrastructure aligns with the latest OCR guidelines. We integrate end-to-end encryption for data at rest and in transit, utilizing AES-256 standards to protect patient records. Our engineering team conducts quarterly business associate agreement reviews, ensuring that 100 percent of third-party vendors meet the rigorous security benchmarks established by the Health Insurance Portability and Accountability Act.
Is Zero Trust architecture necessary for a mid-sized business in North Texas?
Zero Trust is essential for mid-sized firms because 42 percent of security incidents in 2025 originated from compromised internal credentials. Moving beyond traditional perimeter security, this architecture requires continuous verification for every user and device attempting to access the network. It's a critical component for businesses in North Texas that utilize hybrid work models, as it reduces the potential attack surface by 75 percent through strict identity-based access controls.
What is the difference between standard IT support and engineering-grade managed services?
Engineering-grade managed services prioritize proactive system optimization and architectural integrity over reactive break-fix solutions. While standard support might resolve a ticket in 4 hours, our engineering-driven approach focuses on a 0.5 percent failure rate through advanced thermal management and bespoke infrastructure design. This methodology applies the same precision found in aerospace cooling solutions to the IT environment, ensuring that every integrated component operates at peak performance levels.
How often should a Dallas firm conduct a cybersecurity vulnerability assessment?
Dallas firms should conduct automated vulnerability scans weekly and full-scale penetration tests every 180 days. Statistics from the 2025 Texas Cybersecurity Council show that 54 percent of exploits targeted vulnerabilities that were discovered more than 30 days prior to the attack. Regular assessments provide the data-backed insights necessary to maintain world-class security posture, allowing for the immediate remediation of critical patches within a 24-hour window.
Can PWR Technologies help with VoIP migration for offices in Plano and Frisco?
We facilitate seamless VoIP migrations by deploying dedicated 10Gbps fiber links and prioritized Quality of Service protocols. For a typical 50-person office in Plano or Frisco, the migration process takes exactly 14 business days from initial site survey to final hardware deployment. Our engineering team ensures that voice traffic is isolated on a bespoke VLAN, maintaining 100 percent call clarity and eliminating the latency issues common in standard residential-grade configurations.
What happens if our data backup fails during a local Dallas power outage?
Our redundant backup strategy utilizes the 3-2-1-1-0 rule, ensuring that data is replicated to an off-site, Tier IV data center located 200 miles outside the immediate DFW power grid. If local hardware fails, we initiate a failover process that achieves a Recovery Time Objective of less than 15 minutes. This system is tested monthly to guarantee that 100 percent of critical datasets are recoverable even during a total grid collapse or localized electrical surge.
Why is endpoint management a priority for businesses in the DFW Metroplex?
Endpoint management is the top priority because 73 percent of DFW employees now utilize at least three different devices for work-related tasks. By implementing best practices for PWR Technologies LLC, we provide centralized visibility into every laptop, tablet, and smartphone connected to your network. This allows for the immediate remote wiping of lost devices and ensures that 100 percent of endpoints are running the latest security firmware, preventing unauthorized access from unsecured public Wi-Fi.

.png)